Home » Zero Trust Network Architecture: Microsegmentation และ ZTNA
Zero Trust Network Architecture: Microsegmentation และ ZTNA
Zero Trust Network Architecture: Microsegmentation และ ZTNA
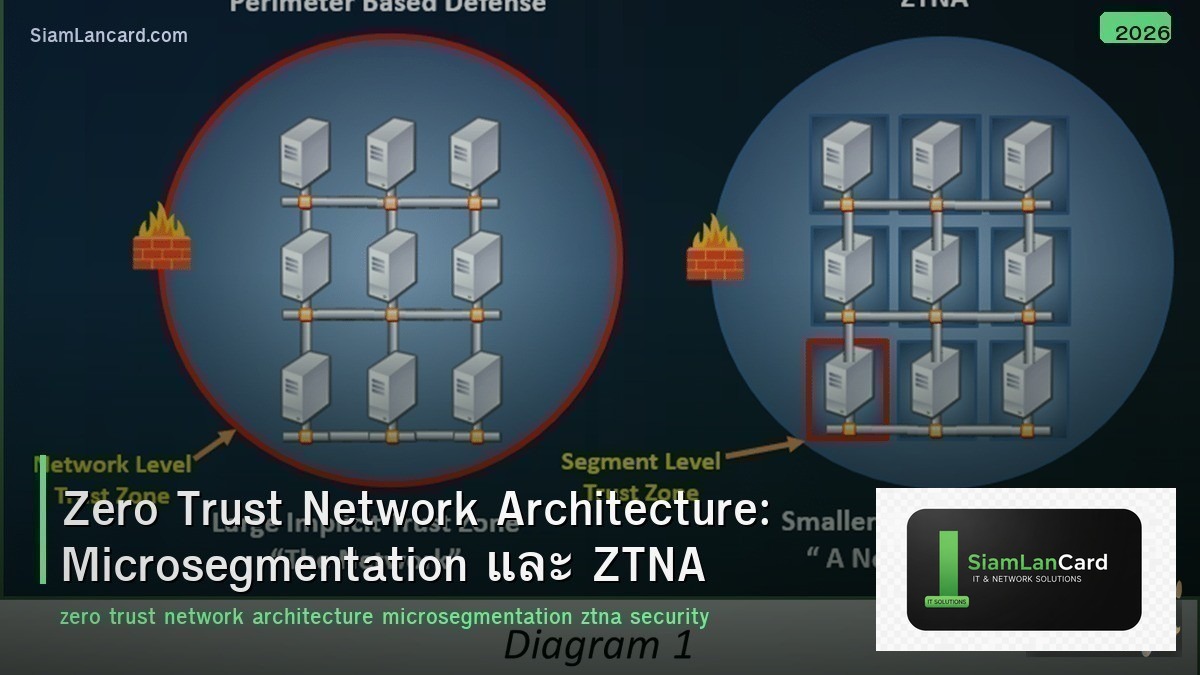
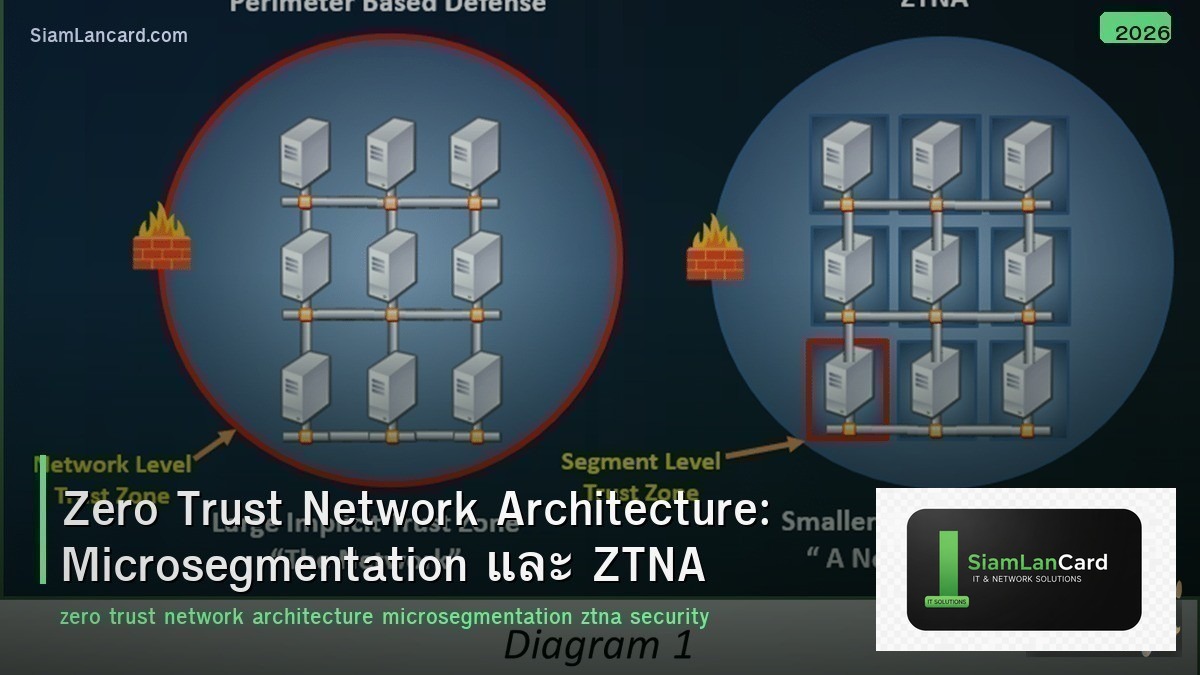
Zero Trust คือ security model ที่ไม่ trust ใครหรืออะไรโดย default — ทุก access request ต้องถูก verify ทุกครั้ง ไม่ว่าจะมาจาก inside หรือ outside network “Never trust, always verify” Microsegmentation แบ่ง network เป็น segments เล็กๆ ที่มี policy เฉพาะ และ ZTNA (Zero Trust Network Access) แทนที่ traditional VPN ด้วย identity-based access
Traditional security ใช้ perimeter-based model (castle-and-moat): trust everything inside the network ซึ่งเมื่อ attacker เข้ามาได้ก็ lateral move ได้ทั้ง network Zero Trust แก้ปัญหานี้: ทุก user/device/application ต้องถูก authenticate + authorize ทุกครั้ง + least privilege access + continuous monitoring
Zero Trust Principles
| Principle |
รายละเอียด |
| Never Trust, Always Verify |
ทุก access request ต้อง authenticate + authorize (ไม่ว่าจะมาจากไหน) |
| Least Privilege |
ให้ access เท่าที่จำเป็น (minimum required permissions) |
| Assume Breach |
Design ว่า attacker อยู่ใน network แล้ว → limit blast radius |
| Verify Explicitly |
ใช้ทุก signal: identity, device health, location, behavior, risk score |
| Continuous Monitoring |
ตรวจสอบตลอดเวลา (ไม่ใช่แค่ตอน login) |
Zero Trust vs Traditional Security
| Feature |
Traditional (Perimeter) |
Zero Trust |
| Trust Model |
Trust inside, block outside |
Trust nothing, verify everything |
| Network Access |
VPN → full network access |
ZTNA → access only specific apps |
| Segmentation |
Few VLANs (coarse) |
Microsegmentation (per-workload) |
| Authentication |
Once at login |
Continuous (every request) |
| Lateral Movement |
Easy (trusted inside) |
Blocked (every hop verified) |
| Remote Access |
VPN (full tunnel) |
ZTNA (per-app, identity-based) |
Microsegmentation
| Feature |
รายละเอียด |
| คืออะไร |
แบ่ง network เป็น segments เล็กๆ (per-workload/per-app) แต่ละ segment มี policy เฉพาะ |
| Granularity |
Per VM, per container, per workload (ไม่ใช่แค่ per VLAN) |
| East-West Traffic |
Control lateral movement (traffic ระหว่าง workloads ภายใน DC) |
| Policy |
Whitelist model: allow only known good traffic → deny all else |
| Enforcement |
Hypervisor-level (NSX), host-based (agents), network-based (firewalls) |
Microsegmentation Approaches
| Approach |
Enforcement Point |
ตัวอย่าง |
| Network-based |
Firewall / switch ACLs |
Cisco ACI contracts, Palo Alto zones |
| Hypervisor-based |
Virtual switch / distributed firewall |
VMware NSX, Microsoft Hyper-V |
| Host-based (Agent) |
Agent on each workload |
Illumio, Guardicore (Akamai), Cisco Tetration |
| Container-based |
CNI / service mesh |
Cilium, Calico, Istio |
| Identity-based |
Tags / labels (not IP) |
Cisco TrustSec SGT, NSX security tags |
ZTNA (Zero Trust Network Access)
| Feature |
VPN (Traditional) |
ZTNA |
| Access Model |
Network-level (full network access) |
Application-level (per-app access) |
| Trust |
Trust after VPN login |
Verify every request (continuous) |
| Visibility |
User on network (invisible apps) |
Apps invisible until authorized (dark cloud) |
| Lateral Movement |
Possible (on same network) |
Blocked (only authorized apps) |
| Device Posture |
ไม่เช็ค (หรือเช็คแค่ตอน connect) |
Continuous posture check (AV, OS patch, compliance) |
| User Experience |
VPN client → connect → access |
Seamless (agent or agentless browser) |
| Scalability |
VPN concentrator bottleneck |
Cloud-native (distributed PoPs) |
ZTNA Vendors
| Vendor |
Product |
จุดเด่น |
| Zscaler |
Zscaler Private Access (ZPA) |
Largest ZTNA, cloud-native, inside-out connectivity |
| Palo Alto |
Prisma Access ZTNA |
Integrated with Prisma SASE, strong security |
| Cloudflare |
Cloudflare Access |
Edge-based, easy setup, developer-friendly |
| Cisco |
Secure Access (Duo + Umbrella) |
Duo MFA + Umbrella SWG + ZTNA integrated |
| Fortinet |
FortiSASE ZTNA |
Integrated with FortiGate, cost-effective |
| Netskope |
Netskope Private Access |
Strong DLP + CASB + ZTNA combination |
Zero Trust Architecture Components
| Component |
Function |
| Identity Provider (IdP) |
Authenticate users (Okta, Azure AD, Ping) |
| MFA |
Multi-factor authentication (something you know + have + are) |
| Device Trust |
Verify device health (MDM, EDR, compliance check) |
| Policy Engine |
Evaluate access request ตาม identity + device + context → allow/deny |
| ZTNA Broker |
Proxy access to applications (user never touches network) |
| Microsegmentation |
Enforce east-west policies (lateral movement prevention) |
| SIEM/XDR |
Continuous monitoring + threat detection + response |
Implementation Roadmap
| Phase |
Action |
| 1. Identify |
Map users, devices, applications, data flows |
| 2. Protect |
Implement MFA + device trust + identity-based policies |
| 3. ZTNA |
Replace VPN with ZTNA สำหรับ remote access |
| 4. Microsegment |
Segment workloads (start with critical apps → expand) |
| 5. Monitor |
Continuous monitoring + analytics + automated response |
| 6. Optimize |
Refine policies based on data + expand Zero Trust to all assets |
ทิ้งท้าย: Zero Trust = Never Trust, Always Verify
Zero Trust Never trust, always verify + least privilege + assume breach Microsegmentation: per-workload policies (block lateral movement) ZTNA: per-app access (replace VPN), continuous verification Verify: identity + device health + location + behavior + risk Implementation: MFA → ZTNA → microsegmentation → continuous monitoring
อ่านเพิ่มเติมเกี่ยวกับ 802.1X NAC RADIUS และ SASE Architecture ที่ siamlancard.com หรือจาก icafeforex.com และ siam2r.com