Home » DDoS Protection: Attack Types, Mitigation, Scrubbing Center, CDN, Rate Limiting และ Incident Response
DDoS Protection: Attack Types, Mitigation, Scrubbing Center, CDN, Rate Limiting และ Incident Response
DDoS Protection: Attack Types, Mitigation, Scrubbing Center, CDN, Rate Limiting และ Incident Response
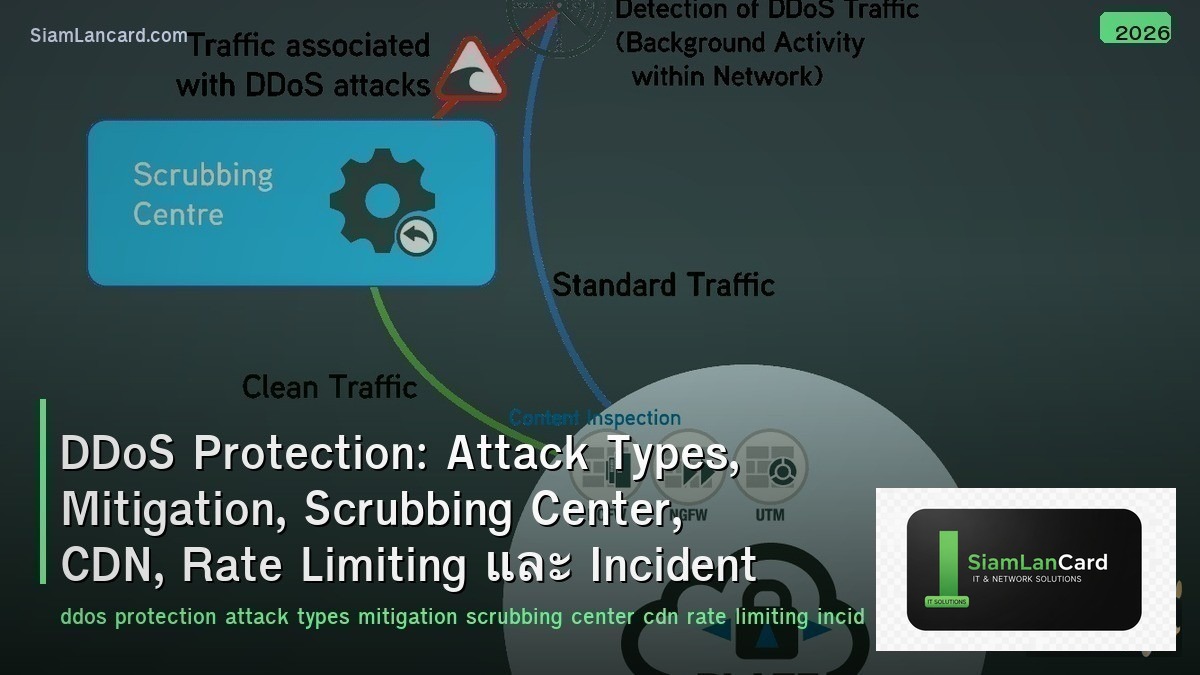
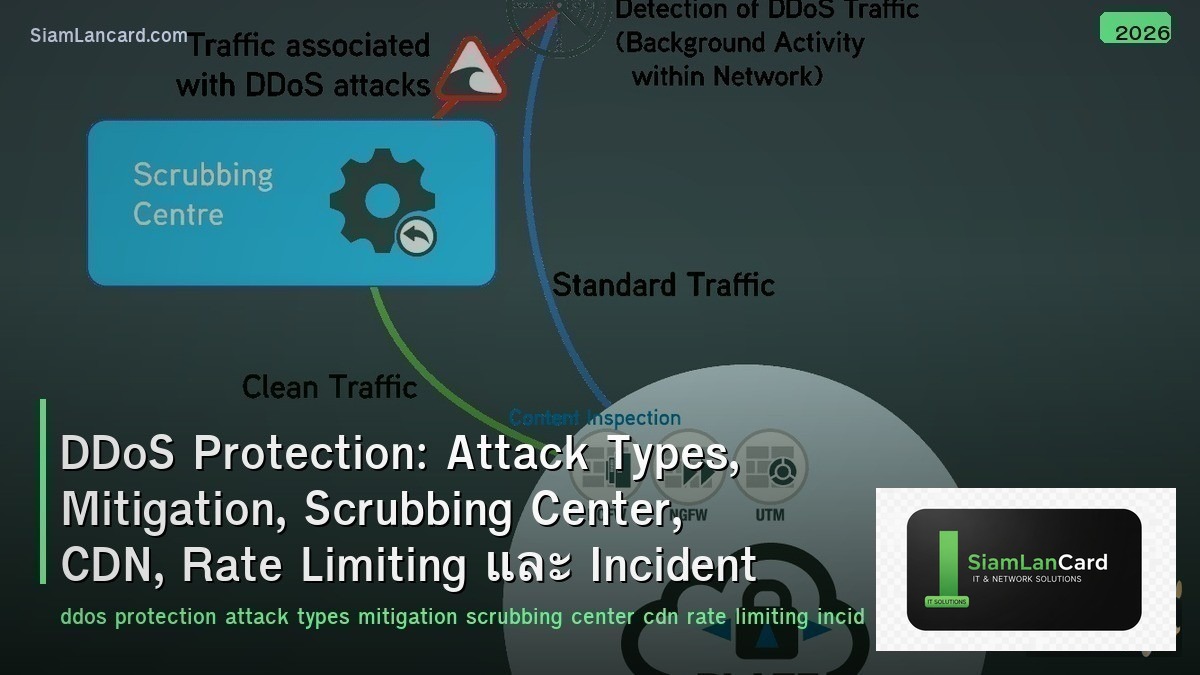
DDoS (Distributed Denial of Service) Protection ป้องกันการโจมตีที่ทำให้บริการล่ม Attack Types มีหลายประเภทตั้งแต่ volumetric ถึง application layer, Mitigation ใช้หลายเทคนิคร่วมกัน, Scrubbing Center กรอง traffic ที่ไม่ดีออก, CDN กระจาย load และดูดซับ attack, Rate Limiting จำกัดจำนวน requests และ Incident Response วางแผนรับมือเมื่อถูกโจมตี
DDoS attacks เป็น ภัยคุกคามที่เพิ่มขึ้นทุกปี: attack size เพิ่มจาก 300 Gbps (2013) เป็น 3.47 Tbps (2023 — Microsoft record), จำนวน attacks เพิ่ม 40%+ ต่อปี, DDoS-as-a-Service ทำให้ใครก็โจมตีได้ ($10-50/เดือน), และ IoT botnets (Mirai variants) มี device หลายล้านตัว ทุกองค์กรที่มี online presence ต้องมี DDoS protection plan
DDoS Attack Types
| Layer |
Attack |
How |
Volume |
| L3/L4 Volumetric |
UDP Flood, ICMP Flood, DNS Amplification, NTP Amplification |
Flood bandwidth with massive traffic volume |
10 Gbps – 3+ Tbps |
| L4 Protocol |
SYN Flood, ACK Flood, TCP State Exhaustion |
Exhaust connection tables on firewalls/servers |
Millions of packets/sec |
| L7 Application |
HTTP Flood, Slowloris, RUDY, API abuse |
Exhaust server resources (CPU, memory, connections) |
Low bandwidth, high impact |
| DNS |
DNS Query Flood, DNS Water Torture, NXDOMAIN |
Overwhelm DNS servers → sites unreachable |
Millions of queries/sec |
| Multi-Vector |
Combination of L3/L4/L7 simultaneously |
Overwhelm multiple defense layers at once |
Most sophisticated, hardest to mitigate |
Amplification Attacks
| Protocol |
Amplification Factor |
How |
| DNS |
28-54x |
Small query → large response (ANY record type) |
| NTP |
556x |
monlist command → returns list of recent clients (huge response) |
| Memcached |
51,000x |
Small request → massive response from cache (UDP port 11211) |
| SSDP |
30x |
UPnP discovery → device responds with large XML |
| CLDAP |
56-70x |
LDAP query over UDP → large directory response |
Mitigation Techniques
| Technique |
How |
Effective Against |
| Scrubbing Center |
Route traffic through scrubbing center → filter bad traffic → forward clean traffic |
All types — primary enterprise defense |
| CDN/Anycast |
Distribute traffic across global PoPs → absorb volumetric attacks by distribution |
Volumetric, L7 HTTP floods |
| Rate Limiting |
Limit requests per IP/session/API key per time window |
L7 application floods, API abuse |
| SYN Cookies |
Don’t allocate state until 3-way handshake completes (stateless SYN response) |
SYN floods |
| BGP Blackhole |
Route attacked IP to null → stops attack but sacrifices the target IP |
Emergency last resort — stops all traffic including legitimate |
| BGP Flowspec |
Distribute filtering rules via BGP → upstream routers drop attack traffic |
Volumetric, protocol attacks — filter close to source |
| WAF |
Web Application Firewall inspects L7 requests → block malicious patterns |
L7 application attacks, bot detection |
| GeoIP Blocking |
Block traffic from countries with no legitimate users |
Reduce attack surface when source countries are known |
DDoS Protection Providers
| Provider |
Capacity |
Key Feature |
| Cloudflare |
248+ Tbps network |
Always-on, free tier available, integrated CDN+WAF+DDoS |
| Akamai (Prolexic) |
200+ Tbps |
Dedicated scrubbing centers, SOC support, enterprise focus |
| AWS Shield |
AWS scale |
Standard (free, L3/L4) + Advanced ($3K/month, L7, DRT support) |
| Azure DDoS Protection |
Azure global network |
Adaptive tuning, cost protection, integration with Azure WAF |
| Radware |
12+ Tbps scrubbing |
Hybrid (on-prem + cloud), behavioral analysis, bot management |
| Imperva |
10+ Tbps |
3-second SLA for mitigation, integrated WAF, API protection |
Incident Response
| Phase |
Action |
| Preparation |
DDoS protection in place, runbook documented, contacts ready, regular testing |
| Detection |
Monitoring alerts: traffic spike, latency increase, server errors → confirm DDoS (not just flash crowd) |
| Classification |
Identify attack type (volumetric/protocol/L7), source (botnet, amplification), target |
| Mitigation |
Activate scrubbing, enable rate limiting, scale resources, BGP diversion if needed |
| Communication |
Notify stakeholders, update status page, contact ISP/provider if upstream help needed |
| Recovery |
Verify services restored, remove emergency rules, document timeline and actions |
| Post-Mortem |
Analyze attack, improve defenses, update runbook, test new mitigations |
ทิ้งท้าย: DDoS Protection = Layered Defense + Preparation
DDoS Protection Attacks: volumetric (bandwidth flood), protocol (SYN flood), L7 (HTTP flood), DNS, multi-vector Amplification: DNS (54x), NTP (556x), Memcached (51,000x) — small request → massive response Mitigation: scrubbing center, CDN/anycast, rate limiting, SYN cookies, BGP blackhole/flowspec, WAF, GeoIP Providers: Cloudflare (248+ Tbps, free tier), Akamai, AWS Shield, Azure DDoS, Radware, Imperva IR: prepare (runbook) → detect (monitoring) → classify → mitigate → communicate → recover → post-mortem Key: DDoS attacks are inevitable for any online business — layered protection + tested incident response = resilience
อ่านเพิ่มเติมเกี่ยวกับ Network Security Architecture Defense in Depth Segmentation และ Network Forensics Packet Capture Flow Analysis Threat Hunting ที่ siamlancard.com หรือจาก icafeforex.com และ siam2r.com