Home » Cloud Networking: VPC, Transit Gateway, Direct Connect, VPN, Cloud Load Balancer และ Multi-Cloud
Cloud Networking: VPC, Transit Gateway, Direct Connect, VPN, Cloud Load Balancer และ Multi-Cloud
Cloud Networking: VPC, Transit Gateway, Direct Connect, VPN, Cloud Load Balancer และ Multi-Cloud
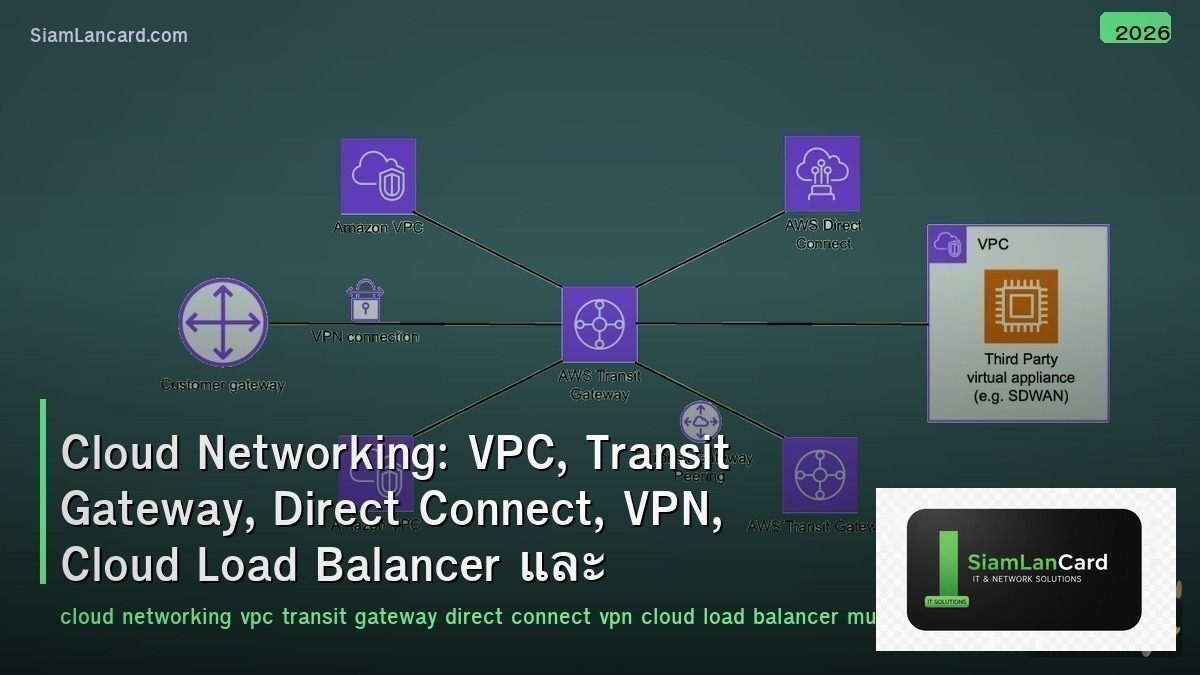
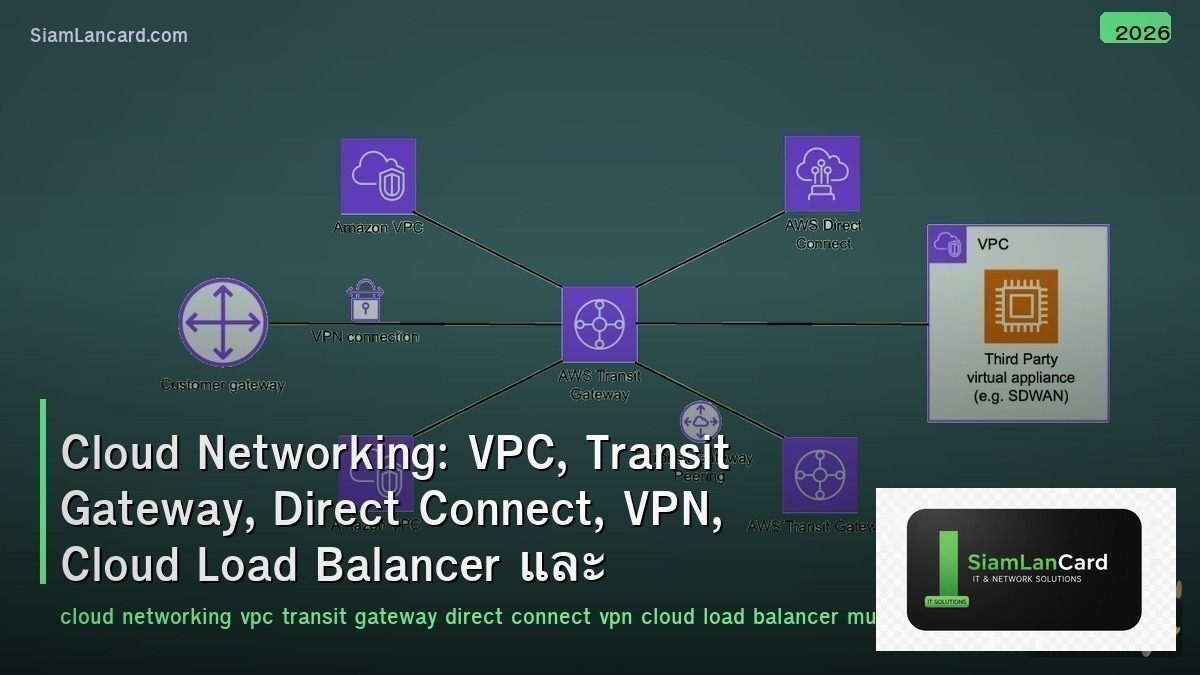
Cloud Networking เป็นโครงสร้าง network บน cloud platforms VPC (Virtual Private Cloud) สร้าง isolated network บน cloud, Transit Gateway เชื่อมต่อ VPCs หลายตัว, Direct Connect/ExpressRoute เชื่อมต่อ on-premises กับ cloud ด้วย dedicated link, VPN เชื่อมต่อผ่าน encrypted tunnel, Cloud Load Balancer กระจาย traffic และ Multi-Cloud ใช้หลาย cloud providers พร้อมกัน
Cloud networking เป็น skill ที่ทุก network engineer ต้องมีในปัจจุบัน: 94% ของ enterprises ใช้ cloud services (Flexera 2024) แต่ cloud networking ต่างจาก on-premises อย่างมาก: ไม่มี physical switches/routers ให้ config, ทุกอย่างเป็น software-defined, networking เป็น API-driven, security model ต่างกัน (security groups vs firewall rules) Network engineers ที่เข้าใจทั้ง traditional networking + cloud networking เป็นที่ต้องการสูงมากในตลาด
VPC (Virtual Private Cloud)
| Feature |
AWS VPC |
Azure VNet |
GCP VPC |
| Scope |
Regional (spans all AZs in region) |
Regional (spans all AZs) |
Global (spans all regions) |
| Subnets |
Per-AZ (public/private) |
Per-VNet (no AZ restriction) |
Per-region (auto-mode or custom) |
| CIDR |
/16 to /28 (can add secondary CIDRs) |
/8 to /29 |
/8 to /29 per subnet |
| Default Routing |
Local route (intra-VPC) + IGW for internet |
System routes + UDR (User Defined Routes) |
Subnet routes + custom routes |
| Security |
Security Groups (stateful) + NACLs (stateless) |
NSG (stateful) + ASG (application) |
Firewall Rules (stateful, global/regional) |
| Peering |
VPC Peering (non-transitive) or Transit Gateway |
VNet Peering (non-transitive) or Virtual WAN |
VPC Peering (within project/org) |
Transit Gateway / Hub-Spoke
| Feature |
Detail |
| Problem |
VPC/VNet peering is non-transitive: 10 VPCs need 45 peering connections (n×(n-1)/2) — doesn’t scale |
| Solution |
Transit Gateway: central hub — all VPCs connect to TGW → any-to-any routing through hub |
| AWS TGW |
Regional hub — supports VPC, VPN, Direct Connect attachments — route tables for segmentation |
| Azure Virtual WAN |
Global hub — hub-spoke with VNet, VPN, ExpressRoute — Microsoft-managed routing |
| GCP Cloud Router |
Dynamic routing with BGP — NCC (Network Connectivity Center) for hub-spoke |
| Segmentation |
Route tables on TGW: shared services VPC routes to all, production isolated from dev |
| Scale |
AWS TGW: 5,000 attachments, 50 Gbps bandwidth per AZ — sufficient for most enterprises |
Hybrid Connectivity
| Method |
Bandwidth |
Latency |
Cost |
Use Case |
| Site-to-Site VPN |
1-1.25 Gbps per tunnel |
Variable (internet) |
Low (pay per hour + data) |
Quick setup, backup link, dev/test |
| AWS Direct Connect |
1-100 Gbps |
Consistent low |
High (port + data transfer) |
Production, large data transfer, compliance |
| Azure ExpressRoute |
50 Mbps – 100 Gbps |
Consistent low |
High (circuit + data) |
Enterprise hybrid, SAP workloads |
| GCP Cloud Interconnect |
10-100 Gbps (Dedicated) |
Consistent low |
High |
Production, large data, multi-region |
| SD-WAN to Cloud |
Variable (aggregate) |
Optimized (path selection) |
Medium |
Multi-cloud, branch-to-cloud, SaaS optimization |
Cloud Security Model
| Layer |
Control |
Example |
| Security Groups (SG) |
Instance-level stateful firewall — allow rules only (implicit deny) |
SG: allow TCP 443 from 10.0.0.0/8 → web server |
| NACL (Network ACL) |
Subnet-level stateless firewall — allow AND deny rules |
NACL: deny all traffic from known bad IP ranges |
| WAF |
Web Application Firewall — L7 protection for web apps |
AWS WAF, Azure Front Door WAF, GCP Cloud Armor |
| DDoS Protection |
Volumetric attack mitigation |
AWS Shield, Azure DDoS Protection, GCP Cloud Armor |
| Private Endpoints |
Access cloud services via private IP (not internet) |
AWS PrivateLink, Azure Private Endpoint, GCP Private Service Connect |
| Flow Logs |
Log all network traffic metadata for analysis |
VPC Flow Logs → CloudWatch/S3, NSG Flow Logs → Log Analytics |
Multi-Cloud Networking
| Challenge |
Solution |
| Connectivity between clouds |
Direct interconnect (AWS-Azure via Megaport/Equinix), VPN tunnels, SD-WAN overlay |
| Consistent networking |
Multi-cloud networking platforms: Aviatrix, Alkira, Prosimo — unified control plane |
| Consistent security |
Cloud-agnostic firewalls (Palo Alto VM-Series), SASE (Zscaler), policy-as-code (Terraform) |
| DNS |
Centralized DNS: Route 53, Azure DNS, or third-party (NS1, Cloudflare) — unified resolution |
| Observability |
Multi-cloud monitoring: Datadog, ThousandEyes, Kentik — single dashboard across clouds |
| Automation |
Terraform (multi-cloud IaC), Pulumi — define networking as code across AWS/Azure/GCP |
ทิ้งท้าย: Cloud Networking = Software-Defined, API-Driven, Security-First
Cloud Networking VPC: isolated network on cloud — subnets, routing, security groups — different per provider (AWS regional, GCP global) Transit: TGW/Virtual WAN/NCC — hub-spoke replaces full-mesh peering — scales to thousands of VPCs Hybrid: VPN (quick/cheap), Direct Connect/ExpressRoute (performance/compliance), SD-WAN (multi-cloud) Security: security groups (stateful), NACLs (stateless), WAF, DDoS protection, private endpoints, flow logs Multi-Cloud: interconnect (Megaport/Equinix), platforms (Aviatrix/Alkira), IaC (Terraform), observability (Datadog) Key: cloud networking is API-driven and software-defined — network engineers must learn cloud-specific constructs + IaC
อ่านเพิ่มเติมเกี่ยวกับ SD-WAN Architecture Overlay Underlay ZTP และ SASE Architecture SD-WAN SSE ZTNA CASB ที่ siamlancard.com หรือจาก icafeforex.com และ siam2r.com